Investigative Reporters & Editors 2017 - Law for independent writers panel
American Intellectual Property Law Association Spring 2017 meeting - Music Copyright Panel
Help us protect the Open Internet: Another Fight for Net Neutrality Begins
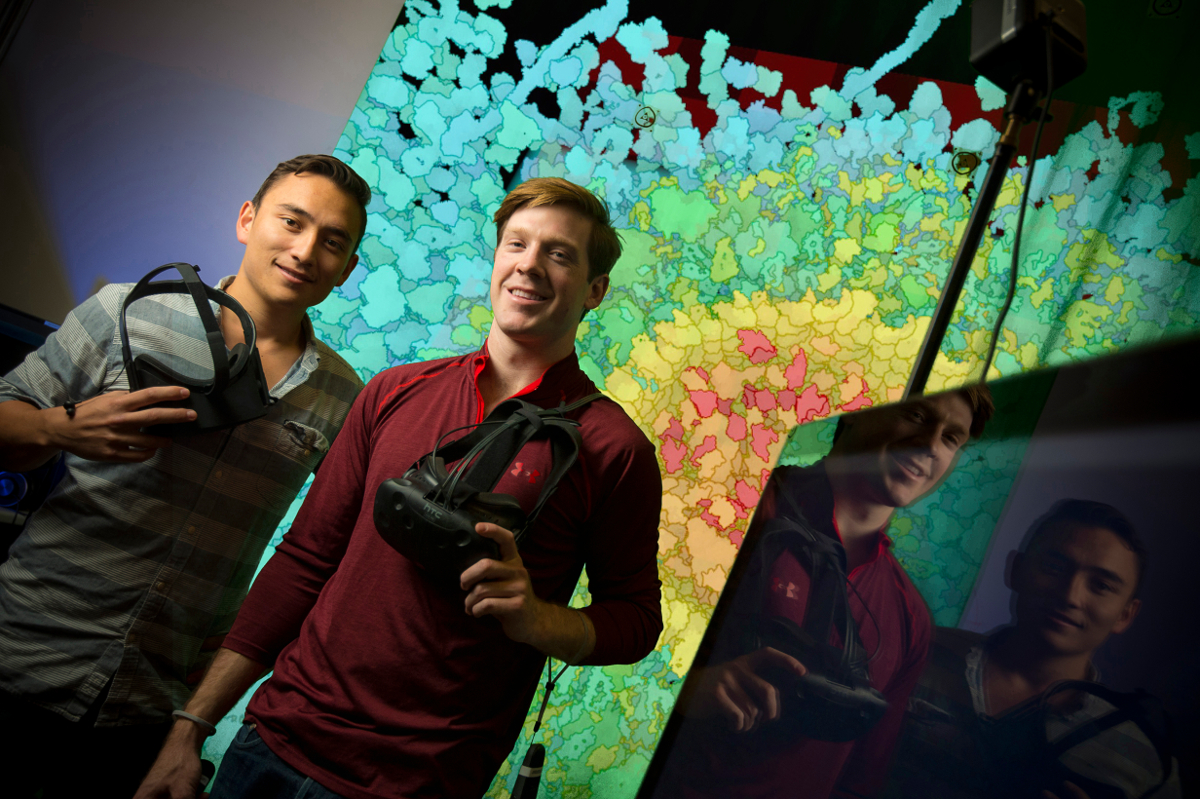
Nanome launches educational virtual reality chemistry and mathematics tool Nano-One on Steam Greenlight!
Film screening: Refugees and cultural stereotyping of Muslims - American Baghdad & Valentino's Ghost - March 29, 2017
It's a WRap! New Media Rights Finishes Working with the Filmmakers of Bad Rap
#FairUseWeek 2017 - Fair use is copyright law's safety valve for free speech
January Newsletter: Protecting journalists, record breaking fundraising, and a film screening
'Painted Nails': A Nail Salon Owner Shares Her Story of Safe Cosmetics Advocacy in New Documentary
Pages
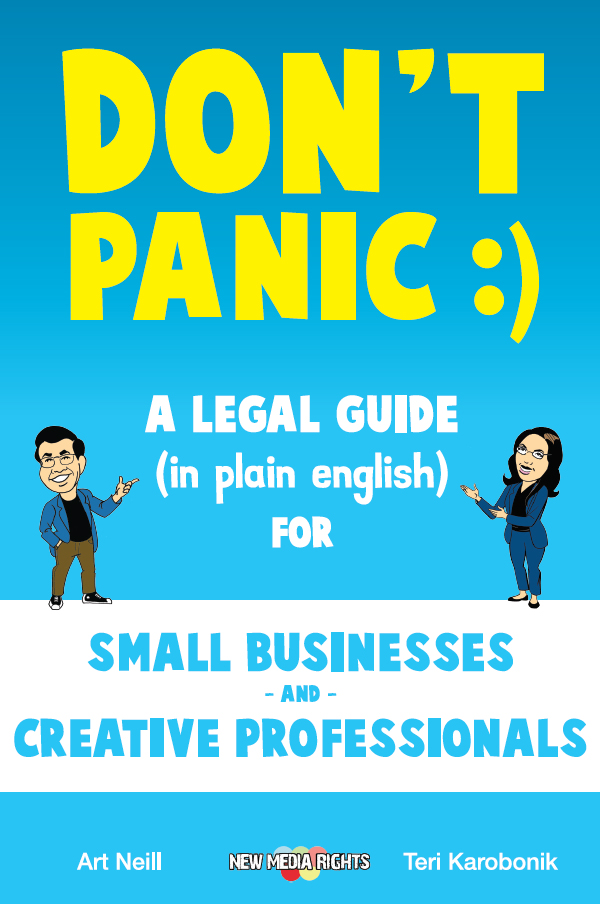
Learn about our legal services for: App Developers, Artists & Graphic Designers, Bloggers & Journalists, Clothing Designers, Entrepreneurs, E-commerce Business People & Startups, Filmmakers & YouTube creators, Public Broadcasting producers,Game Developers, Internet users & Smartphone users, Makers, Musicians, Non-Profits, Photographers, Scholars, Researchers, and Writers and Publishers.